|
Page History
...
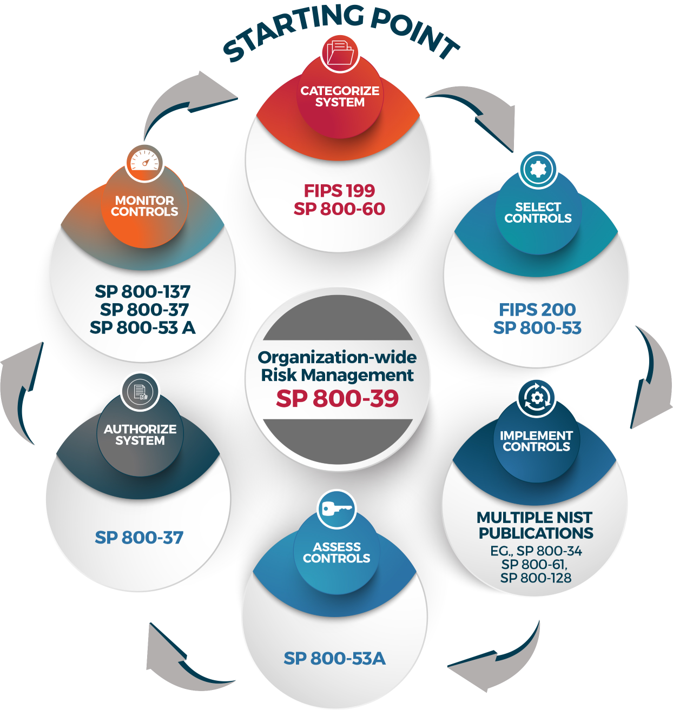
The RMF is the full life cycle approach to managing federal information systems' risk should be followed for all federal information systems. The RMF comprises six (6) phases, with Assessment and Authorization (A&A) being steps four and five in the life cycle. To read more about the RMF, please refer to NIST Special Publication 800-37 , (link is external) Guide for Applying the rev. 2, Risk Management Framework to Federal Information Systems(link is external)for Information Systems and Organizations: A System Life Cycle Approach for Security and Privacy.
|
...
The following general information is intended to help you generally understand the risk management framework, and prepare you to conduct the SA&A for your federal information system or application.
Step 1. Categorize the
...
System
Once you have established that yours is a federal information system, the first step is to categorize the information system. Use the NCI Security Starter Kit for templates and guidance on completing the Federal Information Processing Standard 199 (FIPS)-199) form, the e-Authentication Threshold and Risk Analysis (eTA/eRA) form, the Privacy Impact Assessment (PIA), and the Business Impact Analysis (BIA). All four forms are required to ensure that you properly define the risk rating for your system, and will allow you to select the proper security controls (from NIST 800-53) for your application and will help you design the application to meet security, privacy, and availability needs. This first step is consistent across all federal information systems whether they are hosted internally, externally, or in the cloud.
...